Business Email Compromise attack in the GCC
Business Email Compromise (BEC) has become a common type of attack used to easily gain access to funds from organisations that regularly transfer money to suppliers. These attacks have become common within the Middle East and Gulf Corporation Council (GCC) countries. It is essential for organisations to take adequate precautionary measure to safeguard against these attacks and avoid financial losses, confidential information compromise, reputational damage, and regulatory obligations.
The following real-life case study provides an overview of a recent compromise in the GCC and how Sysprove Consulting supported the organization.
BACKGROUND
In 2019, Sysprove was contacted by a leading manufacturer and supplier with offices in a number of GCC countries. They manufacture and supply stationary to government and private sector establishments. The stationery supplier informed that one of their customers (“the customer”) had transferred money to a fraudulent bank account rather than transferring to their correct account, and suspected that this may be a cyber security incident and requested Sysprove’s assistance
How the attack was conducted
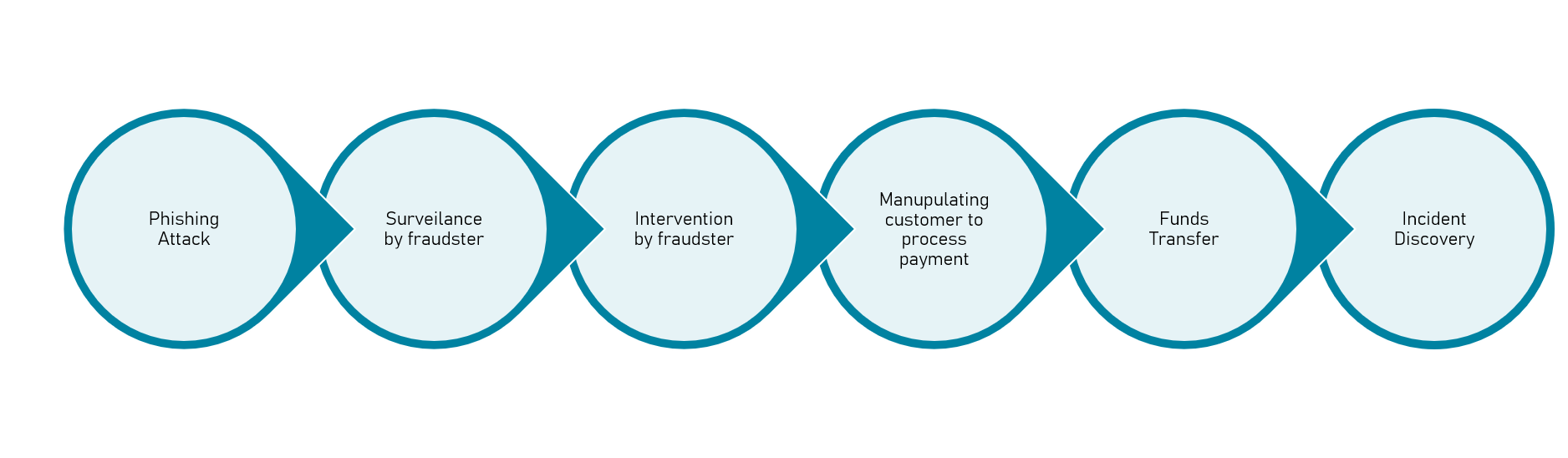

The attackers had specifically targeted both parties (the supplier and the customer) and hacked into their networks where they got access to some email accounts belonging to key personnel of both parties. The attackers have then observed the communication between the two parties and created a domain similar to the legitimate domain of both parties and email accounts that are very similar to the legitimate emails of both the supplier and customer.

Once the emails were set-up, the attackers performed surveillance on the email accounts to identify potential transactions associated with payments which can be manipulated. They intervened by inserting the fake emails into the BCC of the emails sent by the customer to the supplier requesting for supplies. When the supplier received the email request for supplies, they prepared the invoice for the requested items, however as they sent the reply, the attackers were notified of the email before it reaching the customer. The fraudsters modified the invoice by changing the legitimate bank account number to their fraudulent account and forwarded the emails to the customer.

Once the customer received the email with the invoice, they transferred the funds (Over US$ 100,000) to the bank account indicated on the invoice and sent a confirmation email to the supplier indicating that the payment had been processed. The fraudster then replied impersonating the supplier and confirming the payment has been received.

After a while, the customer contacted the supplier directly via phone informing that they have not received their goods, to which the supplier highlighted that the payment has not been processed, it was then that both parties realized they have been victims of a BEC attack
Action taken by the supplier
Performed an internal investigation by tracing back the chain of emails received and sent related to the affected customer
Validated all recent invoices sent to other customers to ensure the fraudsters have not manipulated invoices
Contacted all customers informing them to verify with the supplier directly via a phone call prior to transferring funds especially with respect to large amounts
Performed a security assessment to identify the compromised systems, network, and specific computers
Cyber security awareness sessions for employees conducted by Sysprove Consulting
Upgraded the security systems and and practices
How we can help
- Conduct a cyber security awareness sessions to familiarise employees with cyber threats and provide them with tips to avoid being victims of cyber-attacks.
- Assess the Information Security Governance and security controls within your organisation to ensure they are robust, meet the organisational requirements, and follow industry standards and good practices.
- Review and update current processes, policies, and procedures of the organisation
- Setting up the relevant cyber security incident procedures and standard operating procedures

